Bubble for Enterprise Apps: Why Compliance Will Force You to Migrate
The email lands in your inbox at 4:47 PM on a Thursday.
Subject line: "Security Questionnaire - Vendor Assessment"
Your heart rate spikes. This is it. After six months of relationship building, demos, and pilot programs, the Fortune 500 company you've been courting is ready to move forward. The six-figure contract you've been dreaming about is finally within reach.
You open the 47-page PDF. The first few questions are easy—company size, years in business, insurance coverage. Standard stuff. You scroll down, feeling confident.
Then you hit Section 4: Technical Infrastructure and Data Handling.
"Provide documentation of your SOC 2 Type II certification."
"Detail your data encryption protocols for data at rest and in transit."
"Describe your data residency controls and confirm all EU customer data remains within EU borders."
"Confirm whether your application can be deployed on-premises or within our private cloud environment."
"Provide access to your source code repository for our security team to conduct a vulnerability assessment."
Your confidence evaporates. You stare at the screen, knowing that every honest answer you give will kill this deal.
Because your application runs on Bubble.
And Bubble's shared cloud infrastructure cannot satisfy these self-hosting requirements.
"my client lost a multi-million contract because they ran into compliance issue and they needed the code and DB to be run locally" — vascolucci, Bubble Forum
This isn't a one-off horror story. It's the inevitable collision between no-code convenience and enterprise reality. And if you're building on Bubble with ambitions to serve corporate clients, this collision is coming for you too.
The Enterprise Compliance Wall

Let's be precise about what we're discussing.
Early-stage startups and SMB customers operate differently than enterprise buyers. When you're selling to a 50-person startup, the decision maker might be the CEO who cares about price and features. Security review means "Does it have 2FA?"
Enterprise is different.
When a Fortune 500 company evaluates a vendor, you're not selling to an excited user. You're selling to:
- Procurement teams with standardized vendor assessment frameworks
- Legal departments evaluating contractual risk and liability
- Information security teams conducting technical due diligence
- Compliance officers ensuring regulatory adherence
- IT teams assessing integration and infrastructure requirements
Each of these stakeholders has veto power. And each of them asks questions that Bubble-based applications struggle to answer.
This isn't about bias against no-code. These are legitimate organizational requirements driven by regulation, liability, and hard-learned lessons from security breaches.
The Requirements That Disqualify Bubble
Let's walk through the specific compliance requirements that make Bubble a non-starter for enterprise contracts:
SOC 2 Type II Certification
SOC 2 (Service Organization Control 2) is the baseline security certification for SaaS vendors selling to enterprises. It covers five trust service criteria: security, availability, processing integrity, confidentiality, and privacy.
To achieve SOC 2, you need to demonstrate that you have controls in place. But when your application runs on Bubble, who's actually in control?
- Your database? Bubble's infrastructure.
- Your application logic? Bubble's runtime environment.
- Your deployment process? Bubble's build system.
- Your access controls? Mediated through Bubble's authentication.
You can't get SOC 2 certified for infrastructure you don't control. The best you can do is point to Bubble's own certifications—which shifts the conversation from "your controls" to "your dependency on a third party's controls."
For many enterprise security teams, this isn't acceptable. They need to audit your systems, not trust Bubble's assurances.
HIPAA Compliance
If your application touches protected health information (PHI), HIPAA compliance isn't optional—it's federal law. And HIPAA requires very specific things:
- Business Associate Agreements (BAA): Legal contracts defining responsibilities for PHI
- Access controls: Audit trails for everyone who touches health data
- Encryption requirements: Specific standards for PHI at rest and in transit
- Breach notification: 60-day reporting requirements with specific procedures
Can Bubble handle some of these requirements? In theory, with their Enterprise plan and a signed BAA. But here's the reality: many healthcare enterprises have internal policies that go beyond minimum HIPAA requirements. They mandate data stays on their infrastructure, code can be audited by their security team, and vendors can demonstrate specific technical controls.
When your code is Bubble's proprietary system and your data sits on Bubble's shared infrastructure, these requirements become impossible to satisfy.
GDPR Data Residency
The General Data Protection Regulation requires that European citizens' personal data be handled according to specific rules. For many enterprises, this means data residency requirements: EU data must stay in the EU.
Bubble hosts primarily on AWS infrastructure in the United States. While they offer some EU hosting options, you don't have granular control over where specific data lives. You can't guarantee to a German enterprise client that their users' data never touches US servers.
This isn't about being difficult. Under GDPR, the enterprise is liable if their vendor mishandles EU citizen data. They're not going to absorb that risk for your application when compliant alternatives exist.
On-Premises and Private Cloud Deployment
The most decisive disqualifier: many enterprises require vendors to deploy within their controlled environment.
Banks. Healthcare systems. Government agencies. Defense contractors. Any organization handling highly sensitive data often mandates that applications run within their infrastructure—not on a vendor's cloud, not on a shared platform.
"Enterprise clients won't sign off on Bubble-hosted data"
This single requirement eliminates Bubble from consideration. Not because your application is inadequate, but because the fundamental architecture of Bubble—a multi-tenant platform where your app is a configuration, not a deployable artifact—makes on-premises deployment impossible.
When the enterprise IT team asks "Can we deploy this in our Azure Government cloud?" the answer is no. There's no Bubble application to deploy. There's only access to Bubble's platform.
Source Code Access and Security Audits
Enterprise security teams routinely request access to vendor source code. They want to:
- Conduct vulnerability assessments
- Verify there are no backdoors or security risks
- Understand how sensitive data is handled
- Confirm compliance with their coding standards
With Bubble, you don't have source code. Your application is a visual configuration that Bubble's proprietary system interprets at runtime. You can export the JSON representation of your app, but that's not code—it's a configuration file that only makes sense within Bubble's ecosystem.
When the security team asks for your Git repository, you have nothing to show them.
The Multi-Million Dollar Contracts You're Losing

Let's move from theoretical requirements to actual impact.
"my client lost a multi-million contract because they ran into compliance issue and they needed the code and DB to be run locally" — vascolucci, Bubble Forum
This wasn't a small deal that fell through over a technicality. This was a multi-million dollar contract—the kind that transforms a startup—lost because the enterprise client had a hard requirement for local deployment that Bubble's cloud-only architecture cannot meet.
The client didn't hate no-code. They didn't have an anti-Bubble agenda. They had a compliance policy that required local deployment. When the technical assessment revealed that local deployment was impossible with Bubble's cloud-only model, the contract died.
How many deals like this are dying quietly? How many enterprise sales conversations never even start because the account executive did a preliminary check and saw "built on Bubble" in the technology profile?
"I've lost over 90% of potential clients because I couldn't offer code ownership." — Orbit, Bubble Forum
Orbit spent five years building on Bubble. They understood the platform deeply. And yet, nine out of ten potential clients walked away when they learned the code ownership situation.
Not all of these were lost specifically to compliance issues. But a significant portion were enterprise or enterprise-adjacent buyers who needed self-hosting or on-premises deployment guarantees that Bubble's cloud-only model cannot provide.
The Enterprise Buyer's Calculation
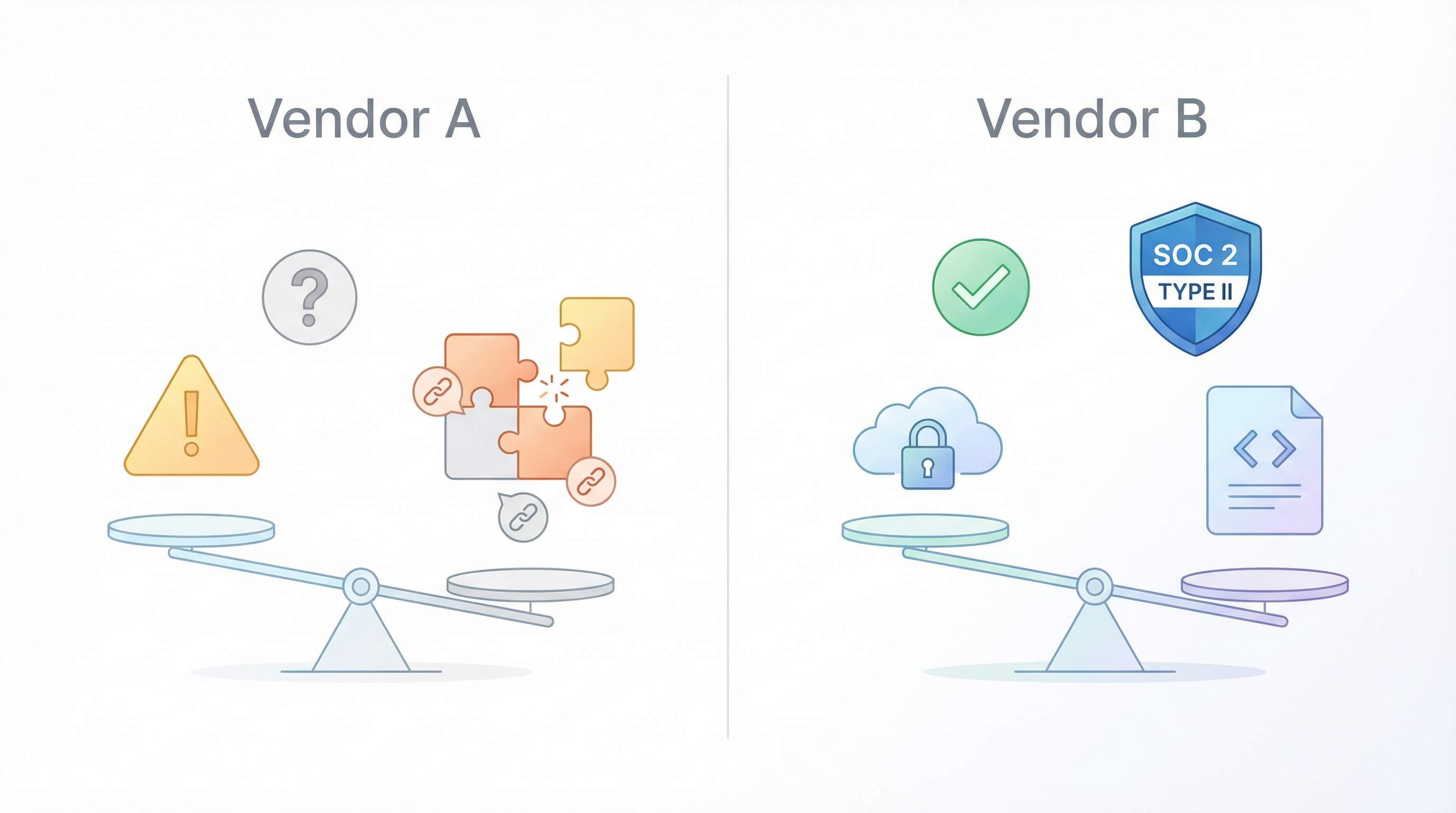
Put yourself in the shoes of an enterprise procurement officer evaluating two vendors:
Vendor A (Your Bubble App):
- Compelling product that users love
- Competitive pricing
- Built on third-party no-code platform
- Relies on Bubble's platform-level SOC 2 certification (app-level certification requires separate audit)
- Cannot deploy on-premises
- Cannot provide source code for security audit
- Data handling governed by Bubble's policies
- Any changes to Bubble's terms/pricing affect the vendor
Vendor B (Custom-Built Application):
- Similar product (maybe slightly less polished)
- Similar pricing
- Own their code and infrastructure
- Has SOC 2 Type II certification
- Can deploy in customer's private cloud
- Provides full source code for security audit
- Full control over data handling
- Independent operation without platform dependency
Which vendor are they choosing?
It's not close. The compliance risk with Vendor A isn't worth the product advantage. Enterprise buyers won't absorb platform dependency risk when alternatives exist.
This is the uncomfortable math: the more successful you become, the more your target customers require self-hosting and infrastructure control that Bubble's cloud-only architecture cannot provide.
The "We'll Cross That Bridge Later" Fallacy

Many founders recognize this problem exists but assume they'll address it when it matters. The reasoning goes:
"We're early-stage. We don't have enterprise customers yet. When we land our first big enterprise deal, we'll figure out the compliance stuff."
This reasoning is dangerous for three reasons:
1. Enterprise Sales Cycles Are Long
By the time you're deep in an enterprise sales process, you've invested 6-12 months of relationship building, demos, and negotiations. Discovering you can't pass security review at the end of that process is devastating—not just financially, but strategically.
You've burned your best shot at that account. They won't re-engage in 12 months after you've migrated. They've already chosen a competitor and signed a multi-year contract.
2. Migration Under Pressure Is Expensive
If you wait until you have an enterprise deal on the table to start migration, you're building under the worst possible conditions:
- Time pressure: The deal has a closing window
- Quality pressure: Rushing increases technical debt
- Resource competition: Everyone wants "urgent" developer attention
- Negotiation weakness: The buyer knows you're scrambling
Planned migration costs $X. Emergency migration costs 2-3X, delivers lower quality, and often misses the deadline anyway.
3. You're Already Losing Deals You Don't Know About
The most insidious impact of compliance limitations isn't the deals that fail in technical review. It's the deals that never start.
When an enterprise account executive qualifies leads, they often do preliminary technology checks. If your company shows up as "built on Bubble" or "no-code platform," some AEs will deprioritize you before the first meeting. They've been burned before. They know the security questionnaire will fail. They focus on vendors they can actually close.
You never hear about these opportunities because the rejection happens before you enter the pipeline.
When Compliance Concerns Become Migration Triggers

Not every Bubble app needs to migrate. But certain indicators suggest compliance-driven migration is inevitable:
Your First Enterprise Pilot Reveals Gaps
The pilot went well. Users love the product. The champion inside the enterprise is pushing for a full rollout. Then legal sends over the vendor agreement with data handling addendums you can't sign.
This is the clearest trigger: you've proven product-market fit with enterprise, but legal/compliance won't let the deal close.
Your Target Customers Are in Regulated Industries
If you're building for healthcare, financial services, government, defense, or education—industries with explicit regulatory requirements—compliance constraints aren't optional. They're built into the buyer's operating environment.
The sooner you have a compliance-ready architecture, the sooner you can pursue these lucrative segments.
Investors Are Asking About Enterprise Readiness
Sophisticated investors understand that enterprise sales require enterprise-grade infrastructure. When they ask "What's your technical roadmap for supporting enterprise customers?" they're probing whether you've thought about this.
"We'll stay on Bubble and see what happens" is not a compelling answer.
Your Customer Success Team Reports Lost Deals
If you have any sales process visibility, track why deals fail. If "couldn't pass security review" or "compliance requirements not met" appears more than once, you have a pattern—not an exception.
The Compliance-Ready Migration Path
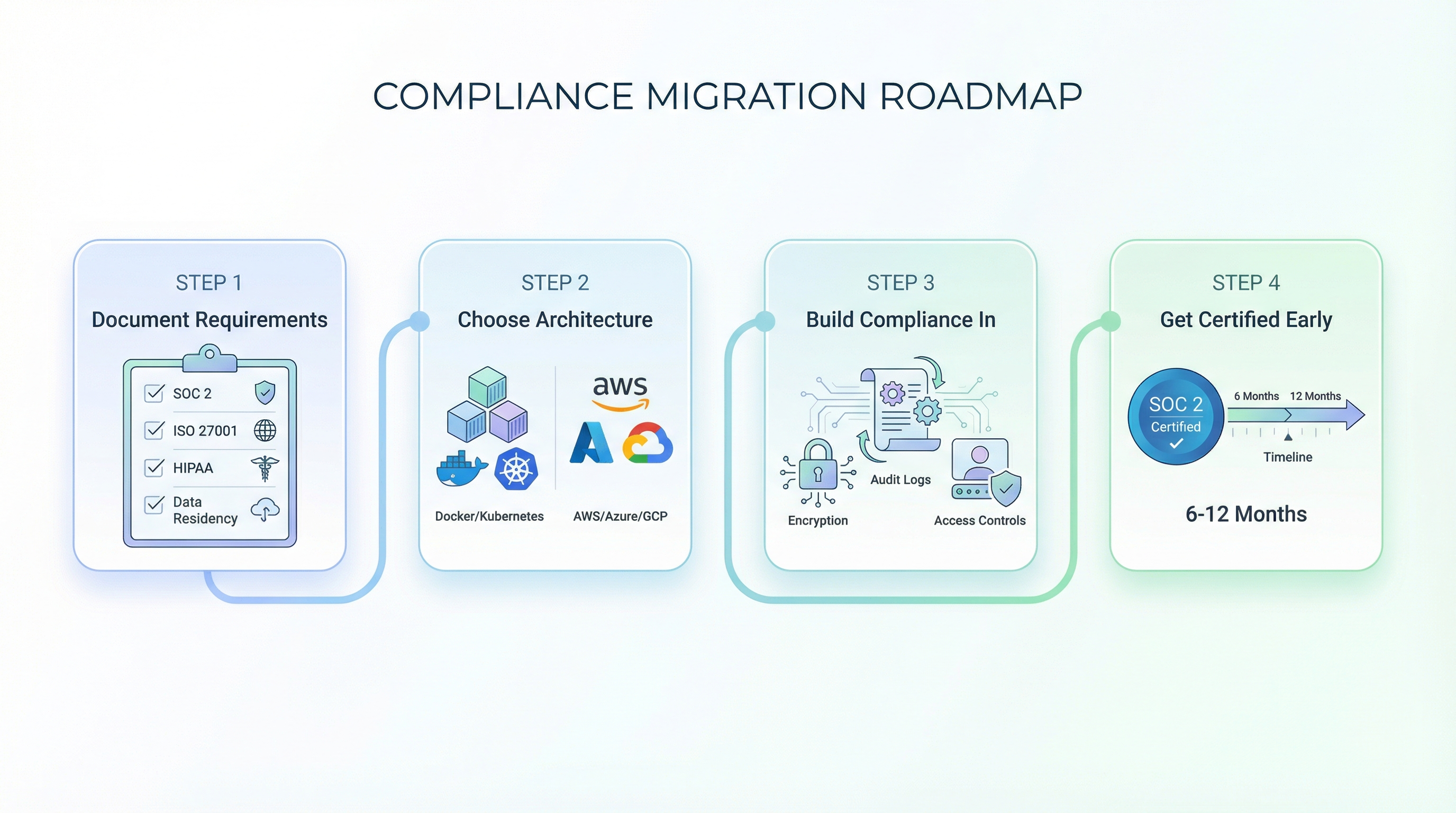
If compliance requirements are driving your migration decision, here's how to approach it strategically:
Step 1: Document Your Compliance Requirements
Not all compliance frameworks are equal. Before migrating, clearly understand what your target customers require:
- Which certifications do they expect (SOC 2, ISO 27001, HIPAA)?
- What data residency requirements exist?
- Is on-premises deployment a must-have or nice-to-have?
- Will they require source code access?
- What penetration testing or security audit expectations exist?
This documentation shapes your target architecture. Over-engineering for requirements you don't need is wasteful. Under-engineering means you hit the same wall with a different technology.
Step 2: Choose an Architecture That Enables Compliance
The right migration target isn't just "any custom code"—it's an architecture designed for your compliance requirements:
| Requirement | Architecture Implication |
|---|---|
| SOC 2 Type II | Cloud infrastructure with audit logging, access controls |
| HIPAA | Specific encryption standards, BAA-capable hosting, audit trails |
| GDPR data residency | Region-specific deployment capability |
| On-premises | Containerized, self-hosted deployment option |
| Source code audit | Clean, documented, auditable codebase |
For most compliance-conscious migrations, this means:
- Containerized deployment (Docker/Kubernetes) for portability
- Major cloud providers (AWS, Azure, GCP) with compliance certifications
- Standard technology stacks (Next.js, PostgreSQL) with security track records
- Infrastructure as code for reproducible, auditable environments
Step 3: Build Compliance Into the Migration Process
Don't migrate first and add compliance later. Bake compliance requirements into the migration specification:
- Encryption standards defined upfront
- Audit logging architected from day one
- Access controls built into the authentication layer
- Data handling policies reflected in database design
A compliance-aware migration costs slightly more than a basic migration but far less than retrofitting compliance onto an existing codebase.
Step 4: Get Certified Before You Need It
SOC 2 Type II certification takes time—typically 6-12 months from initial readiness assessment to certification. Don't wait until an enterprise buyer asks for it.
If enterprise sales are on your roadmap, start the certification process early. Having SOC 2 in hand before the sales conversation dramatically shortens enterprise sales cycles.
The Cost of Delayed Migration

Let's quantify what waiting costs:
Lost Revenue from Disqualified Deals
Every enterprise contract you can't pursue represents lost revenue. If your average enterprise deal is $100K ARR and you lose 2-3 opportunities per year to compliance disqualification, that's $200-300K in annual revenue you're forfeiting.
Over a 3-year delay, that's potentially $600K-900K in cumulative lost revenue—far more than migration costs.
Negotiation Weakness in the Deals You Can Close
Even when you close enterprise deals despite Bubble limitations, you're negotiating from weakness. The buyer knows you can't serve their compliance-demanding peers. They extract better pricing, more favorable terms, and shorter contract lengths because your leverage is limited.
Compounding Technical Debt
Every feature you build on Bubble while knowing you'll eventually migrate adds to the migration scope. The longer you wait, the more complex the migration becomes, and the more you've invested in architecture you'll abandon.
Competitive Disadvantage
While you're explaining why you can't pass security review, your competitors—who've already migrated—are closing deals and building relationships. Enterprise customers have long memories. The vendor they choose now often becomes the incumbent for years.
The Path Forward

If you're building on Bubble with enterprise ambitions, the question isn't whether compliance will force migration—it's when.
The founders who navigate this successfully share common patterns:
-
They acknowledge the limitation early. They don't pretend enterprise compliance is a solvable Bubble problem.
-
They plan migration proactively. They start migration planning before the first enterprise deal falls through, not after.
-
They choose compliance-ready architectures. They migrate to technology stacks designed for the requirements they'll face.
-
They treat migration as investment, not cost. They understand that compliance-ready infrastructure opens revenue opportunities that exceed migration costs.
Enterprise compliance requirements aren't going away. If anything, they're intensifying as data breaches make headlines and regulations expand. SOC 2 is becoming table stakes. GDPR enforcement is increasing. New regulations emerge regularly.
The no-code platform that enabled your rapid MVP becomes the ceiling that limits your growth. That ceiling is measured in compliance requirements—and those requirements are ultimately measured in contracts you win or lose.
The choice is whether you hit that ceiling in a carefully planned migration, or in a desperate scramble after watching your biggest deal fall apart.
Ready to Become Enterprise-Ready?
BubbleExport converts your Bubble application into production-ready code that you own completely—enabling SOC 2 certification, HIPAA compliance, on-premises deployment, and full source code access for enterprise security audits.
Get a free migration assessment → Book a consultation
We'll analyze your Bubble application, identify your compliance requirements, and provide a detailed migration roadmap to enterprise readiness.
Ready to talk migration?
Get a free assessment of your Bubble app. We'll tell you exactly what to expect — timeline, cost, and any potential challenges.